Overview
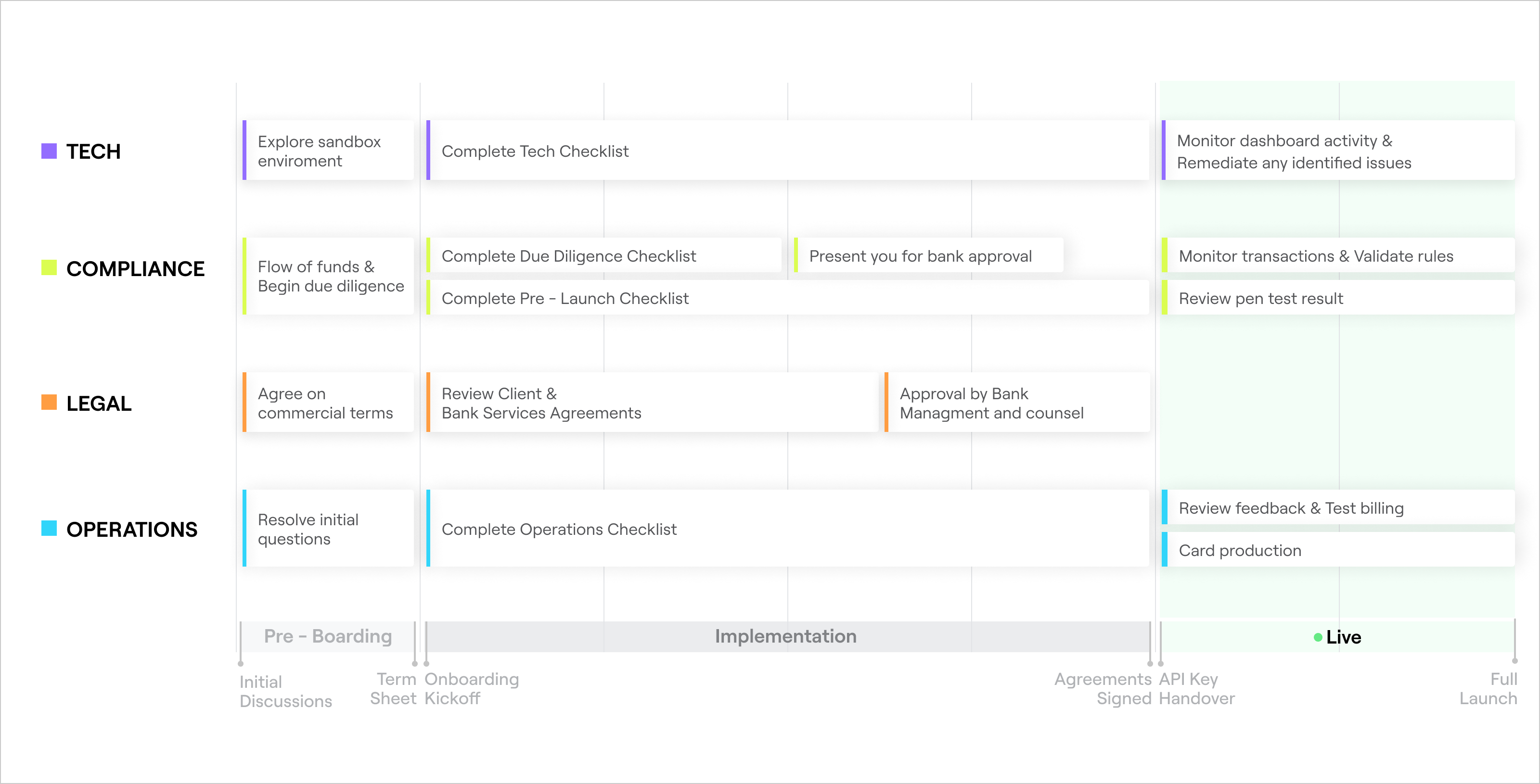
Onboarding Timeline
Tech Checklist
You will need to implement the following items before Unit hands over the API keys to the production environment.
| Item | Explanation | Guidance |
|---|---|---|
| User Authentication | You should use a secure authentication solution to authenticate End Users before accessing your end-user application with the banking services. | Suggested vendors include Auth0, AWS Cognito, or Firebase. |
| Phone Number Verification | For security and fraud prevention purposes, you must verify the phone number provided as part of a Unit banking application before creating the application. | We recommend using Twilio Verify. This checklist item is satisfied if you use Unit's Application Form |
| Second Factor Authentication | For security and fraud prevention purposes, you must authenticate the customer with a second factor before performing various sensitive actions. See 2 Factor Authentication section of our documentation for further details. | We recommend using Unit’s Customer Token Verification. |
| Idempotency | Unit uses idempotency to protect against repeat occurrences of sensitive operations (e.g. originating an ACH Credit). Such operations are marked in our API docs. |
|
| ACH Debit Authorization | Before you can originate an ACH Debit (i.e. pull funds from a counterparty at another bank), you must authenticate and collect consent from this counterparty. | We require using Plaid for authentication followed by the counterparty's explicit consent in order to debit an outside account. The counterparty's consent must be retained for 2 years following the termination or revocation of the debit authorization. We also require the use of Plaid Identity and Plaid Balance. For use cases that require other solutions, please contact Unit for approval. |
| Firewall | Implement a web application firewall in front of your web application. | We recommend using one of: AWS WAF, Azure Web Application Firewall, Google Cloud Armor or Cloudflare. |
| Storage Encryption | Whenever possible, we recommend that you avoid storing the Personally Identifiable Information (“PII”) of your customers. However, if you do store PII, it must be encrypted at rest. | PII includes any information that could be used to identify an individual, including:
|
| Card Management APIs | If issuing cards, implement Unit's Card Management APIs. | Implement the following card APIs in your UI: activate card, set pin, change pin, report card lost/stolen, close card, and replace card. This checklist item is satisfied if you use Unit's Card Component |
| White-Label Fraud Outreach | If issuing cards, configure your settings for reaching out to customers about potentially fraudulent transactions. | Please see our detailed guide here. |
| Statements | Regulations require that you allow End Users to retrieve monthly account statements for every account they own. | Ensure you can access the relevant monthly statement information through Unit’s API and present it to the End User through your app or site. ⇨ Unit minimizes the work you need to do by offering a white-label Account Component and Statements API. |
| Terms & Conditions (“T&Cs”) & End User Onboarding | You must collect End User consent to relevant T&Cs before calling the Unit API to create applications. T&Cs should be displayed clearly on all devices, typically in the footer of your website. You must display certain disclosures during the account opening process and in all marketing materials. |
⇨ See Compliance Pre-Launch Checklist for further guidance. This checklist item is satisfied if you use Unit's Application Form |
Compliance Checklist
Due Diligence
Before we present you to the bank partner for formal approval, we need the following information from you.
| Item | Explanation | Guidance |
|---|---|---|
| Complete Due Diligence Questionnaire | You must complete this questionnaire, which requests basic background information about your organization, your business model, and customer base. | You may complete the questionnaire before your due diligence call with the compliance team, or the compliance team can complete it with you during the call. ⇨ You can find this questionnaire in your Client Folder. |
| Provide Security Information | You must demonstrate you have implemented a system to ensure your systems are secure and any vulnerabilities have been addressed. You will need to provide us with a copy of your organization’s:
|
|
| Provide Business Continuity Information | You must demonstrate that you have a business continuity plan in place to address threats to your business like system outages and natural disasters. |
|
| Provide Vendor List | You must provide Unit with a list of all vendors, along with an assessment of each one’s criticality to your organization and the risk each poses to your operations. | Criticality may be related to, but is not equal to, risk. For example, AWS may be critical to your operations, but its redundancies and high availability may make it a low-risk vendor. ⇨ Your list of accounts payable is often a good place to find all your vendors. |
| Provide Financials | You will need to provide Unit with your current financial statements. | Unit’s minimum requirement is that you have 12 months of capital to sustain your current burn rate. ⇨ Two years of audited financials are preferred, but we accept a 12-month history of your balance sheet and a P&L statement. |
| Provide Pitch Deck | You will need to provide basic documentation so we can better understand your product and company. | In particular, you will be asked to provide:
|
Pre-Launch
Before we hand over API keys to the production environment (i.e., before you are able to onboard customers), you must complete the following items.
| Item | Explanation | Guidance |
|---|---|---|
| Ensure Sufficient Insurance Coverage | You must purchase insurance coverage that meets Unit’s requirements to ensure you are properly protected against unforeseen challenges or negative events. | Unit requires the following types of insurance:
⇨ See the Insurance Guide for further guidance. |
| Develop T&Cs | You must develop relevant T&Cs and collect End User consents, including:
| Unit offers template T&Cs that you may use, but you must review and finalize them with us and your counsel before going live. After the due diligence call, Unit will draft your T&Cs and share with you for your review. ⇨ Review the T&Cs item in the Tech Checklist above. |
| Develop End User Disclosure | You must display a disclaimer on any webpage, mobile app or marketing material that discusses a financial product. Most clients display disclosures as a footer of their website or mobile application. |
|
| Confirm ACH Authorization | If your customers can initiate an ACH debit, you must provide the proper ACH disclosures. | The compliance team will work with you to draft this disclosure during the Onboarding process, if needed. ⇨ You can find template ACH Authorization disclosure in your Client Folder. |
| Onboard Your Organization | You will need to complete our CIP process to formally onboard your organization onto the Unit platform. | The link to complete this process is https://apply.unit.co/. |
| Review the Deposit Agreement | You will need to agree to Unit’s Deposit Agreement prior to funding your Reserve Account and onboarding customers. | We will send this agreement to you via DocuSign once you have successfully onboarded your organization to the Unit platform. |
| Fund Your Reserve Account | You will need to fund your Reserve Account according to the terms set out in your Client Services Agreement before onboarding any customers. | ⇨ Please contact Unit for further guidance on the Reserve Account. |
Penetration Testing
Before reaching 50 customers on Unit or within 3 months after the API key handover, you are required to provide the results of a recent and valid penetration test.
Penetration tests will be required annually thereafter. Penetration test providers must be approved by the Unit security team to ensure the quality and scope of the test. Please see more details below.
| Item | Explanation | Guidance | |
| ------------------------------------------------------------ | ------------------------------------------------------ | ------------- |
| Penetration Test Type| There are three primary types of penetration testing: black box, gray box, and white box.
In gray or white box testing, the tester is provided with valid credentials, allowing them to test flows that require authentication. This enables the tester to identify and evaluate potential security vulnerabilities in areas that would otherwise be inaccessible in black box testing. |
- Unit accepts only Gray box or White box penetration testing.
The provided test accounts should have access to all the internal and external APIs (especially APIs involving financial related actions)| Penetration tests should cover:
- Network (Internal and external)
- Web application
- Mobile applications (if applicable)
- Other APIs (e.g. application login, reset password, and other business flows provided as part of the customers’ solution.)
- The penetration testing report must have been conducted within the past 12 months.
- Our customers will be mandated to perform a penetration test at least once every year.
- The full version of the report must be shared without any masked or hidden sections.
Alternatively, you can select a different vendor for the test. Choosing a different vendor will require approval from Unit’s Security team that can be received after sharing the vendor’s name, the testing scope, and the testing methodology.|
- Unit requires the test to be performed by one of Unit’s approved penetration test vendors or a vendor of your choice that was pre-approved by our Security team.
- All medium and above vulnerabilities identified must be fixed and retested by the penetration tester.
- Our information security team will review the results of the penetration test to assess the severity of any identified vulnerabilities and determine if any further remediation is required.
- If the results are satisfactory (no medium or high findings) or include a sufficient mitigation plan, we do not require another full test. However, we do require a connection-focused penetration test before you reach 50 customers. The focus of this test is the addition of Unit functionality and the effects it will have on you and+ your customers.
- If the results are not satisfactory (some medium or high findings) and do not include a sufficient mitigation plan, we will require a full penetration test following launch and before you reach 50 customers, including a test of your connections to Unit.
- We will require a full penetration test following launch and before you reach 50 customers, including a test of your connections to Unit.
Operations Checklist
| Item | Explanation | Guidance |
|---|---|---|
| Ensure Customer Support process is set up | You will need to set up a Customer Support process prior to onboarding customers. | You will need to set up a Customer Support process and select an appropriate tool (e.g. ZenDesk) so that customer support tickets can be routed through your interface to Unit. ⇨ See the Customer Support Guide for further guidance. |
| Submit card design | You will need to develop and submit a card design template to begin the card issuance process. | You will work on the card design and issuance process with Unit’s operations team. ⇨ See the Card Issuance Guide for further guidance. |
